News
HPE DevOps Report: Security Hindered by Pressure to Release Apps Quickly
- By David Ramel
- October 25, 2016
In an age of huge data breaches and hacked IoT devices bringing down the Internet, it seems strange that enterprise developers still need to be reminded of the importance of security, but that's exactly what Hewlett Packard Enterprise does in its new DevOps research.
Specifically, HPE sought to find out how organizations are transitioning to DevOps and how security efforts fit in this process while discovering the obstacles to employing secure DevOps and opportunities for improvement in its new "Application Security and DevOps" report (free PDF download).
One finding that's likely no surprise to enterprise developers everywhere: security concerns are often at odds with the pressure on developers to quickly release apps for business reasons.
As the very term DevOps means different things to different people, HPE characterized it as having to do with: integrated development, IT, and QA teams; automated testing; frequent deployment; and other traits.
Whatever it means, DevOps is the future, according to research firm Gartner Inc., which predicted 50 percent of enterprises will be practicing the methodology by year's end.
In assessing how security practices are being used in this growing movement, HPE eschews traditional DevOps/security initiatives such as "Rugged DevOps" and "DevSecOps" in favor of the term, "the secure SDLC" (software development life cycle). This emphasizes the baked-in integration of security in the process, rather than treating it as an optional approach like Rugged DevOps and DevSecOps do, HPE said.
Furthermore, HPE said it looks at both the promise and reality of the secure SDLC, as opposed to others who just predict that DevOps will enable better development security practices.
"The reality of adoption has proven to be different from the promise," the report stated. "When asked how organizations adopting DevOps are currently protecting applications, the overwhelming majority cited security practices or controls downstream of the SDLC, with only 20 percent stating that secure SDLC testing is done throughout development. Most organizations are relying on the technologies downstream, such as pre-production penetration testing and network security. A shocking 17 percent stated that they are not using any technologies to protect their applications."
 [Click on image for larger view.]
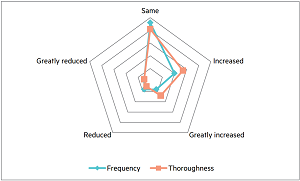
How DevOps Has Affected Application Security (source: HPE)
[Click on image for larger view.]
How DevOps Has Affected Application Security (source: HPE)
The primary barrier to implementing better DevOps security practices is structional in nature, HPE said.
"We found that the key factor hindering security adoption within DevOps is organizational barriers," the report stated. "While one of the main promises of DevOps is the collaboration between development, operations, and quality assurance (QA), security teams are often nowhere to be found in the DevOps conversation or team.
"Overall, developers and IT Ops care about security but feel it is already under control or that it's someone else's issue (such as security, InfoSec and compliance departments)," the report said. "Security feels disconnected from both development and operations, and in some cases, respondents admitted to not even knowing their security teams. Reporting lines within organizations do not help break down organizational silos and most development, operations, and security groups have completely separate reporting structures. These dynamics can lead to a divide between security organizations and development with differing metrics and misaligned priorities."
Another dichotomy concerns the competing goals of developers -- pressured by business concerns to ship apps quickly -- and security pros, who typically want to slow things down to make sure everything is safe.
"Most developers today do care about security and many are starting to learn and incorporate security practices in their work, but they are still primarily measured and motivated to focus on timely delivery, features and quality," the report stated. "They usually agree that there is an overall lack of security training and pressure to release quickly compromises their ability to place more emphasis on software vulnerabilities until it is too late in the process."
It doesn't help that security isn't included in most academic computer science programs or in job requirements, or that there's a security skills shortage. Facing all these factors, developers are in a crunch.
"Developers are under immense pressure to get features out to market as fast as possible," the report said. "A 2015 Forrester study concluded, 'customer expectations in competitive markets rise in response to attractive alternatives. Organizations in these markets are scrambling to keep pace. 73 percent of IT decision-makers surveyed said that business leaders demand more-frequent delivery.' This business requirement is forcing development to prioritize features, functionality, and performance and eliminate anything that is considered to slow down the development process."
The HPE study in some ways closely resembles a similar research effort published this summber by F5 Networks Inc., titled "Application Security in the Changing Risk Landscape." In covering that study, we reported on F5's conclusion: "Hiring and retaining skilled and qualified application developers will improve an organization's security posture." The report went on to say: "Sixty-nine percent of respondents believe the shortage of skilled and qualified application developers puts their applications at risk. Moreover, 67 percent of respondents say the 'rush to release' causes application developers in their organization to neglect secure coding procedures and processes."
HPE, meanwhile, said: "While 99 percent of those surveyed agree that DevOps is an opportunity to improve application security, only 20 percent said that appsec testing is being done during development."
To address such concerns, HPE concluded its new report by outlining the following best practices to achieve a secure SDLC:
- Security should be a shared responsibility across the organization to eliminate barriers.
Security must be embedded throughout every stage of the development process, with
executive support and metrics to hold teams accountable for secure development.
- Bridge awareness, emphasis and training gaps by making it seamless and more intuitive
for developers to practice secure development. Organizations should integrate security tools
into the development ecosystem to allow developers to find and fix vulnerabilities in real-time as
they write code. This makes it easy and efficient to develop securely, and educates the developer
on secure coding in the process.
- Leverage automation and analytics as application security force multipliers.
Organizations should leverage enterprise-grade application security automation with analytics
built in to automate the application security testing audit process and allow their application
security professionals to focus only on the highest priority risks. This reduces the number of
security issues that require manual review, saving both time and resources, while lowering
overall risk exposure.
HPE developed the report based on quantitative studies and qualitative surveys and interviews conducted by a third party.
About the Author
David Ramel is an editor and writer at Converge 360.