News
Adwind RAT Is Back, Used To Attack 400K Systems
- By John K. Waters
- February 9, 2016
An infamous Remote Access Trojan (RAT), a piece of Java-based malware that gives attackers a backdoor into Windows, Linux, Mac OS X and Android devices, has re-emerged -- after apparently being shut down last year -- now as a commercial "malware-as-a-service" platform.
Known variously through several rebrandings as Frutas, Unrecom, Sockrat, jRat, AlienSpy, Adwind and JSocket, the Java-based, cross-platform RAT has been in development since 2013. The latest version is available as of this writing on the JSocket Software Web site.
The Java-based malware platform targets systems supporting the Java Runtime Environment (JRE), providing what its author reportedly describes as "rich capabilities for remote control, data gathering, data exfiltration and lateral movement." According to researchers at Kaspersky Labs, the RAT has been used to attack more than 400,000 systems over the past three years. In a blog post, Kaspersky's chief security expert, Alexander Gostev and Vitaly Kamluk, director of the company's Global Research and Analysis Team, reported receiving a sample of the malware via e-mail from some banks in Singapore on behalf of "a major Malaysian bank." The researchers traced the IP address of the e-mail senders to a server in Romania and a mail server and account to a company located in Russia.
The Kaspersky researchers report that the JSocket RAT's codebase is the same as the Adwind RAT, making it likely that both were authored by the same person. The JSocket RAT is currently available via online subscription, with prices ranging from $25 for 15 days to $300 a year. The buyers get technical support, obfuscation services to evade antivirus detection, virtual private network accounts, and free scans with multiple antivirus engines.
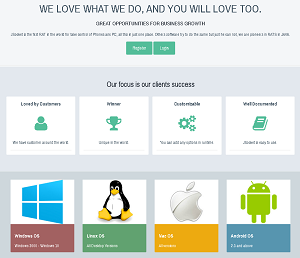 [Click on image for larger view.]
The JSocket Software Site, Advertising a RAT (source: JSocket Software)
[Click on image for larger view.]
The JSocket Software Site, Advertising a RAT (source: JSocket Software)
"The malware program operates by sending out system information and accepting commands from a remote attacker," they explained. "These commands can be used, among other things, to display messages on the system, open URLs, update the malware, download/execute files, and download/load plug-ins. A significant amount of additional functionality can be provided through downloadable plug-ins, including such things as remote control options and shell command execution."
"We would like to encourage enterprises to review the purpose of using a Java platform and to disable it for all unauthorized sources," they added.
Fidelis Security exposed the AlienSpy RAT in a report published last April, and Internet domain registrar GoDaddy suspended AlienSpy's domains shortly thereafter, which seemed to kill it. But the new JSocket version appeared last June, and it has been updated at least twice since that release.
Kaspersky believes that the author is Spanish speaking. It's clear from the Web site that English is not the author's first language. On the "How to Buy" page on the JSocket Software site, he/she writes: "We need make a account. You need go to https://jsocket.org/page/registration." As of this writing, that link is broken.
The Kaspersky researchers published an infographic entitled "A Brief History of the Adwind RAT Malware" along with the blog post.
"RAT" is an acronym that can also stand for "Remote Access Tool" and "Remote Administration Tool."
About the Author
John K. Waters is the editor in chief of a number of Converge360.com sites, with a focus on high-end development, AI and future tech. He's been writing about cutting-edge technologies and culture of Silicon Valley for more than two decades, and he's written more than a dozen books. He also co-scripted the documentary film Silicon Valley: A 100 Year Renaissance, which aired on PBS. He can be reached at [email protected].